Configuration SSO
April 26, 2026 at 11:05 PMOn the SSO configuration page you have to enter the required information if you want to use NTLM or Kerberos for single sign-on.
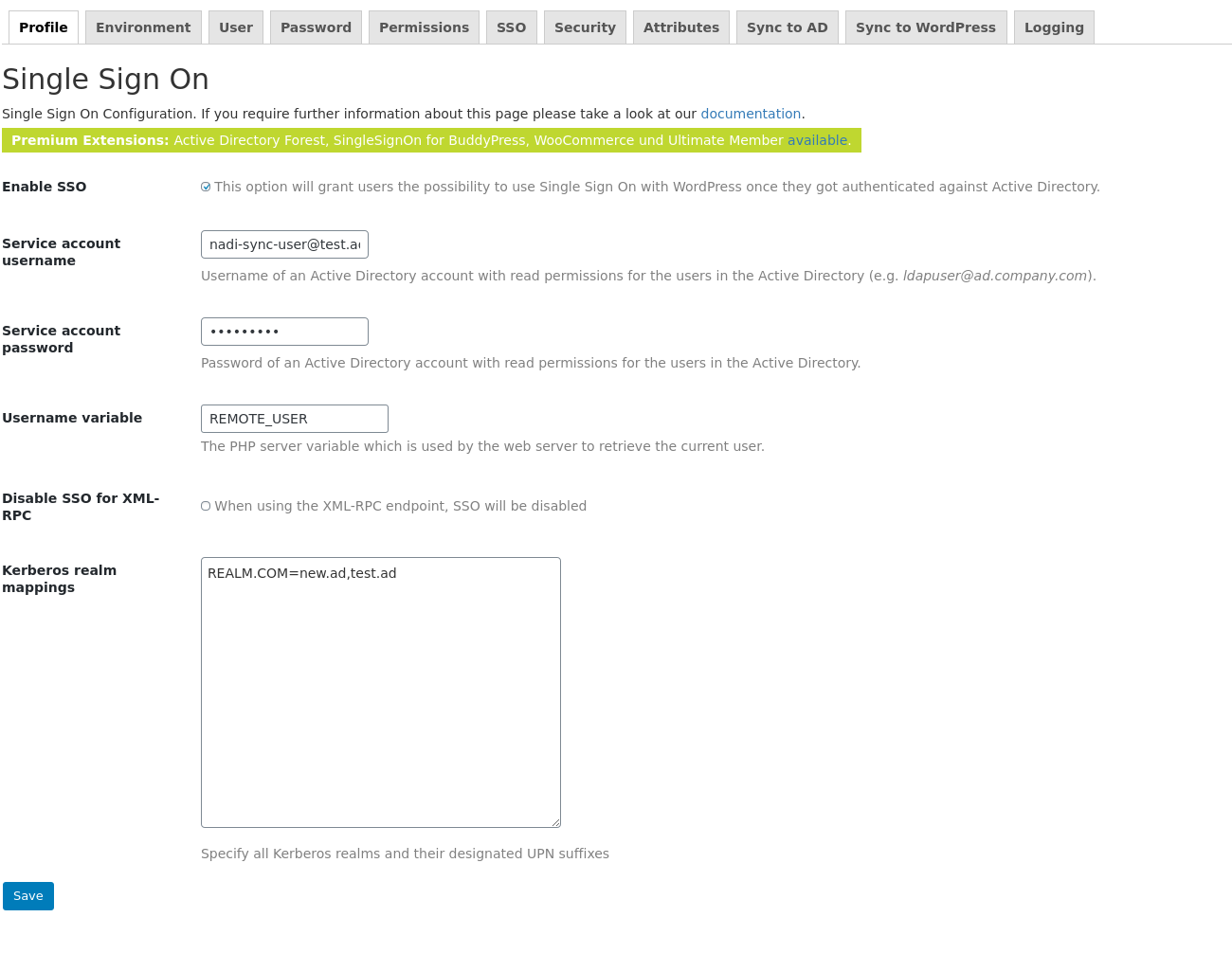
Single Sign On
Enable SSO
This option grants users the possibility to Single Sign On on WordPress. The user has to be previously authenticated by the webserver or frontend proxy. After the user has opened the WordPress site NADI checks for the existence of the Username variable. If it is available, the user is automatically authenticated and his account data is retrieved from the Active Directory.
Service account username
The service account is required to authenticate/re-authenticate/authorize a previously SSO authenticated user. You have to add a service account with read permission in the Active Directory. Please enter the full user information including the domain suffix. The option User Append suffix has no influence on this option.
Service account password
This option defines a new password for the SSO service account.
Username variable
This option defines the server variable which will be used to retrieve the current user. In most cases (Apache, IIS) this should be set to REMOTE_USER. Please consult your webserver’s documentation for more information.
Disable SSO for XML-RPC
since 2.1.9
If you want to make tools like Live Writer working in an SSO environment, SSO must be deactivated for XML-RPC as Live Writer does not work with Kerberos or NTLM.
Kerberos realm mappings
since 2.2.0
This option must be configured if you want to enable Kerberos
- using a Global Catalog configured as your domain controller inside NADI
- inside a multi-domain Active Directory (Forest) environment
- with atleast one sAMAccountNames present in multiple domains inside the forest
In smaller AD environments, the Kerberos realm is most likely identically to the UPN suffix. In AD forests with multiple domain trusts, this is not always the case. In addition to that, the same sAMAccountName can be used in multiple domains of the forest.
Imagine the following configuration:
| Kerberos realm | UPN suffixes | sAMAccountName | Kerberos principal |
|---|---|---|---|
| AD1.COM | our-ad1.com, our-ad1.de | user1 | user1@AD1.COM |
| AD2.COM | our-ad2.com, our-ad2.de | user1 | user1@AD2.COM |
As soon as user1@AD1.com hits the webserver, NADI searches the Global Catalog for the sAMAccountName user1. The Global Catalog will return two results: for user1@AD1.COM and for user1@AD2.COM.
To prevent wrong assignments, you have to map the Kerberos realm AD1.COM to our-ad1.com and our-ad1.de.
Each line must have the format
${KRB_REALM}=${upn_suffix_1},${upn_suffix_2};
e.g. for multiple mappings:
AD1.COM=our-ad1.com,our-ad1.de;
AD2.COM=our-ad2.com,our-ad2.de
or for a single realm mapping:
AD1.COM=our-ad1.com,our-ad1.de