Technical details Active Directory internals Account Lockout Policy
April 26, 2026 at 11:05 PMActive Directory has a group policy settings called Account Lockout Policy. With help of this policy, the Active Directory automatically locks out accounts with a number of failed login attempts.
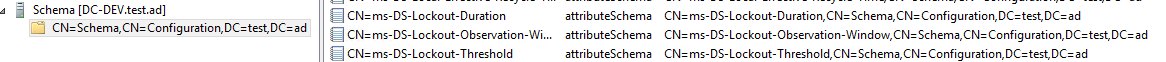
Internally, they are declared in the LDAP Schema partition:
By default, the policy settings are not configured.
You can configure the policy settings by using the Group Policy Editor (gpedit.msc). The settings below Computer Configuration > Policies > Windows Settings > Security Settings > Account Policies > Account Lockout Policy have to be applied to your active Domain Policy. After the domain policy has been applied, the LDAP attributes will be configured below the LDAP tree CN=Password Settings Container,CN=System,DC=YOUR_DOMAIN.
You can configure the following settings:
| Setting | Default | Internal LDAP attribute | Description |
|---|---|---|---|
| Account lockout duration | not configured | MsDS-LockoutDuration |
Duration in minutes how long the account gets locked. A value of 0 means that the account has to be unlocked by an administrator. |
| Account lockout threshold | not configured | MsDS-LockoutThreshold |
Amount of failed login attempts after which the account get locked. With each failed login attempt a counter for this user account will be incremented. |
| Reset account lockout counter after | not configured | MsDS-LockoutObservationWindow |
Amount of minutes after the counter of failed login attempts for the user account is resetted. |
NADI users can be affected by this Group Policy settings as WordPress logins will be forwarded to the Active Directory. If the user enters an invalid password in WordPress, NADI sends the credentials to Active Directory’s LDAP endpoint which then notifies the AD about the failed login attempt. The account lockout counter will be incremented.